我们使用机器学习技术将英文博客翻译为简体中文。您可以点击导航栏中的“中文(简体)”切换到英文版本。
用于运行以太坊验证器的 亚马逊云科技 Nitro Enclaves — 第 1 部分
在本系列文章中,我们为提供质押池和质押即服务的节点运营商提供了使用
在这篇文章(第 1 部分)中,我们解释了为什么
在代码示例
在
以太坊权益证明和验证器
公共区块链的协议和共识设计、实现语言和智能合约功能各不相同。
确定如何激励外部参与者加入网络并运行自己的节点是植根于博弈论的经济设计原则的关键,在博弈论中,你要将网络设计得更加分散,同时提高稳定性。
为了确保验证者的行为诚实,每个验证者必须将32个
用户可以通过多种方式参与以太坊质押:
-
- 运行自己的验证器节点 — 用户运行和维护验证器节点,每个验证人有 32 个 ETH 可以作为抵押品存入。用户可以完全控制节点和验证器密钥。
- 使用质押即服务提供商 ——用户仍然为每个验证人提供 32 个 ETH,但将运营方面的工作转移给运行验证器节点并为用户维护验证器密钥的节点提供商。
- 加入质押池 ——用户可以质押任意数量的以太币。用户质押的 ETH 被汇集在一起,验证器节点由受托的第三方运行。对于没有32 ETH或不愿意质押该金额的用户,此选项很有吸引力。
在第一种情况下,用户实现了所有奖励,而在其他两种情况下,提供商可能会将一定比例的奖励作为其服务的付款。
保护验证器密钥的重要性
运行以太坊验证器节点对以太坊网络的健康至关重要,但会带来潜在的安全风险。验证者密钥(公钥和私钥)用于收集和提取 32 个 ETH 抵押品以及已收集的任何奖励。以太坊的
您可以使用诸如
由于为以太坊共识层引入了
以下解决方案主要针对提供质押池和质押即服务的节点运营商。个人质押者也可以采用该解决方案,但如果他们仅质押最低数量的以太币,则可能会发现运行该解决方案的成本高得令人望而却步。
解决方案概述
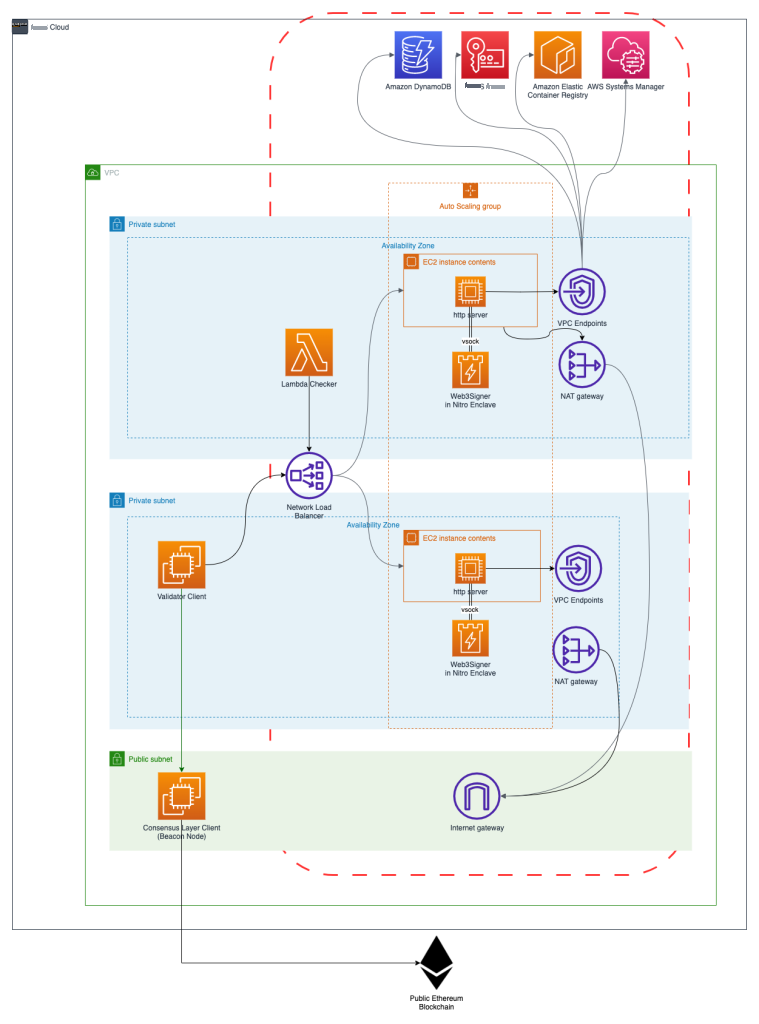
下图说明了我们基于 Nitro Enclaves 的验证器签名服务的架构。
Nitro Enclaves 使用
虚拟机管理程序将安全区的 CPU 和内存与父实例隔离开来,只为父实例和安全区之间的通信提供安全的本地通道 (
每隔 12 秒,就会向以太坊网络提出一个新区块。这被称为
Web3Signer 将使用
在我们的架构中,Web3Signer 在 Nitro 飞地中运行。值得注意的是,在安全性方面,Web3Signer 运行时由 Nitro Enclave 提供,因此可以免受攻击或风险,例如内存转储或文件系统权限不足。尽管如此,通过vsocket将Web3Signer的HTTPS REST API暴露给VPC,引入了与应用程序本身相关的新潜在攻击向量,而像Nitro Enclaves这样的安全运行时环境是无法缓解的。这些攻击向量需要一组不同的衡量标准,例如防止公共 API 访问或高级身份验证机制,例如
本文的下一节详细介绍了如何解密私钥并将其加载到 Nitro Enclave 中的 Web3Signer 中。
为了确保高可用性,Web3Signer 亚马逊弹性计算云 (Amazon EC2) 实例部署在跨多个可用区的自动扩展组中。这些实例从 DynamoDB 加载相同的验证器密钥。网络负载均衡器 (NLB) 将签名请求转发到其中一个实例。多个验证器客户端可以连接到同一 NLB。
托管 Nitro Enclaves 的 EC2 实例不应公开访问,因此应位于私有子网中。EC2 实例可以通过 NAT 网关安全地访问出站互联网,以便下载操作系统更新和其他软件包。在生产环境中,更新和其他依赖关系可以由自定义
与 亚马逊云科技 KMS 或 DynamoDB 等 亚马逊云科技 服务的通信不应穿越互联网,因此应通过放置在每个可用区子网内的
此外,提供的
引导和签名流程
下图描述了部署在 EC2 实例内的组件以及与 DynamoDB 和 亚马逊云科技 KMS 等外部 亚马逊云科技 服务的一般通信流程。

通常,有两个先决条件:
-
一个或多个以太坊验证器密钥已加密并存储在 DynamoDB 中。要安全地生成和加密以太坊验证器密钥,请参阅
在 亚马逊云科技 上使用无服务器架构 安全地低成本生成以太坊验证器密钥 。 出于测试目的,随附的 亚马逊云科技 CDK 代码的演练部分提供了类似的功能。 -
Web3Signer 的 TLS 密钥对已加密并存储在 DynamoDB 中。随附的 亚马逊云科技
CDK 代码的自述部分提供了有关如何生成 TL S 密钥对的说明。
以下步骤详细解释了以太坊认证 和
- 如果所有配置工件都存在,则安全区可以启动。
- 所有文物都以加密方式传递到飞地。
-
由 Nitro Enclave 服务团队提供的工具 kmstool- enclave cli 可在安全区内部使用加密认证来解密配置工件。 -
加上加密认证文档的解密请求通过 亚马逊云科技 提供的 vsock-proxy 路由到 亚马逊云科技 KMS。 - 所有解密的配置工件都存储在内存文件系统的安全区中。
-
Web3Signer 流程开始了。使用提供的 TLS 密钥对和以太坊 2 私钥成功启动安全区后,
https_proxy 将充当在安全区内运行的 Web3Signer 的 HTTPS 端点。 - Web3Signer API 端点现在可以向 EC2 实例外部公开,并且能够处理传入的签名请求,例如,来自以太坊 2 验证器节点的请求。
- 签名请求通过 vsock 连接以加密方式在安全区内转发。验证客户端和 Web3Signer 之间的 TLS 连接在安全区内停止,从而实现端到端的加密传输。
有关 vsocks 隧道上的 HTTPS 和引导过程的更多详细信息可以在本系列的
在配置方面,您不应将多个验证器客户端配置为相同的验证器密钥。这样做很有可能为不同的区块提案签署证明书,或者在同一个时段内提出不同的区块。这些活动将导致
结论
在这篇文章中,我们简要介绍了Nitro Enclaves,并解释了为什么 Nitro 非常适合运行以太坊验证器。我们还解释了使用 Nitro Enclave 的高级引导和签名过程。
您可以按照位于
作者简介
 David-Paul Dornseifer
是 亚马逊云科技 全球专业解决方案架构师组织的一名区块链架构师。他专注于帮助客户设计、部署和扩展端到端的区块链解决方案。
David-Paul Dornseifer
是 亚马逊云科技 全球专业解决方案架构师组织的一名区块链架构师。他专注于帮助客户设计、部署和扩展端到端的区块链解决方案。
 Aldred Hal im
是 亚马逊云科技 全球专业解决方案架构师组织的解决方案架构师。他与客户紧密合作,设计架构和构建组件,以确保在 亚马逊云科技 上成功运行区块链工作负载。
Aldred Hal im
是 亚马逊云科技 全球专业解决方案架构师组织的解决方案架构师。他与客户紧密合作,设计架构和构建组件,以确保在 亚马逊云科技 上成功运行区块链工作负载。
*前述特定亚马逊云科技生成式人工智能相关的服务仅在亚马逊云科技海外区域可用,亚马逊云科技中国仅为帮助您发展海外业务和/或了解行业前沿技术选择推荐该服务。